Introduction
The Basic Malware RE room on TryHackMe consists of three static analysis challenges.
Strings1
Challenge information:
This executable prints an MD5 Hash on the screen when executed. Can you grab the exact flag?
So our goal is to find the plain text input to an md5 hash algorithm. Lets load the binary in IDA.
After loading the binary in IDA, we see the contents of the start function.
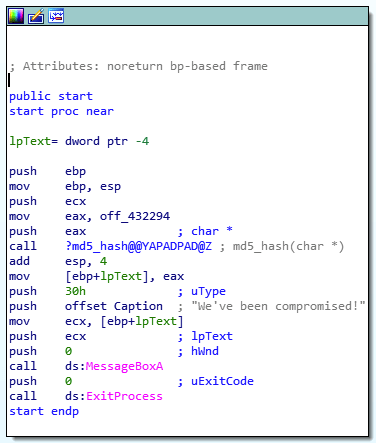
Here we see a call to what seems like a md5 hash function that takes a char pointer as input: call ?md5_hash@@YAPADPAD@Z ; md5_hash(char *)
And if we take a look at the previous operations we can see that the contents of off_432294 is moved into eax, which in turn are pushed on the stack. So lets take a look at the data at off_432294.

Entering the flag in the room we get an Correct Answer message.
Strings2
As with the previous challenge our goal is to find the plain text used to generate an md5 hash. After loading the binary in IDA we are presented with the start function.
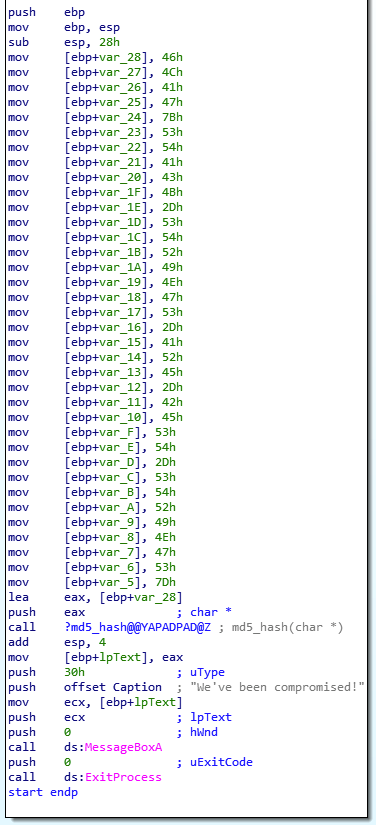
Here we can see that a bunch of values are assigned to a bunch of stack variables before being assigned to eax, which in turn are pushed onto the stack before the call to the md5 hash function.
So if we convert the hex values into ascii values we get the correct flag.

Strings3
Same as before, our goal is to find the plain text flag. When loading the binary in IDA we see the start function.

Here we can see a call to LoadStringA before calling the MD5:digestString function.
Looking at the imports tells us where the function is imported from.

So LoadStringA is imported from USER32.
Taking a look at the documentation for LoadStringA gives us some more information about the usage.
So lets take a look at what parameters are used to call LoadStringA.

- The instance handle (hInstance) is NULL.
- The identifier (uID) is set to the stack variable uID.
- The read buffer (lpBuffer) is set to the stack variable Buffer.
- The buffer size (cchBufferMax) is set to 1023 (0x3FF).
Now we need to find out what uID is, and as we can see the value is written right before we start to push our parameters for the LoadStringA call.

This is basically just an obfuscated hard coded value. So lets go through the steps to get the correct value.
mov eax, 1 ; eax = 1 shl eax, 8 ; eax = 1 << 8 = 256 xor edx, edx ; edx = 0 inc edx ; edx = 0 + 1 = 1 shl edx, 4 ; edx = 1 << 4 = 16 or eax, edx ; eax = 256 or 16 = 272 mov [ebp+uID], eax ; uID = 272
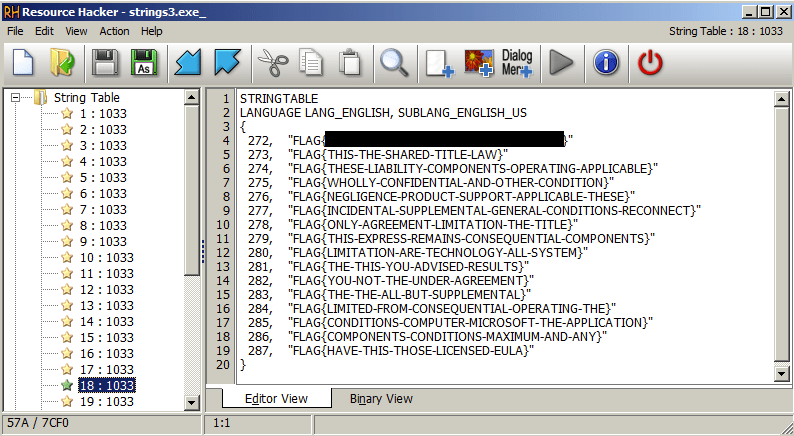
So the Buffer variable is set to the string with ID 272 in a String-table resource. Lets find out what value is stored at that ID.
Opening the binary in Resource Hacker and locating the string-table entry with id 272 gives us the flag.

sorry, probably a dummy question as I new to reverse engineer
for string3
how you get “shl eax, 8 ; eax = 1 << 8 = 256" ??
LikeLike
Since eax is 1 and the shl eax, 8 moves the bits in eax eight steps to the left, i.e.
eax = 0000000000000001 (1 in decimal) and after the shl eax, 8, eax will be 0000000100000000 (256 in decimal)
LikeLike